Triple Entry Accounting (2024) (MDPI's JRFM PDF)
Abstract. Classical double entry accounting has provided the foundation for accounting within the firm for many centuries. The digitally signed receipt, an innovation from financial cryptography, gives rise to exactly duplicated entries for each of 3 parties or roles, the outcome of which we call triple entry accounting. This presents a challenge to double entry bookkeeping by expanding the use of accounting from inside firms to activity between the firms. When applied to digital cash and digital assets, the approach of negotiating a single signed receipt between parties lowers costs by delivering reliable data to support stronger accounting, and makes much stronger governance possible in a way that positively impacts on the future needs of corporate and public accounting. By turning the opinions of firm owners into facts agreed between firms, triple entry bookkeeping creates the bulletproof accounting layer to support aggressive uses and adversarial users such as are found in the Bitcoin system of transactions.

MDPI's Journal of Risk and Financial Management has now published this updated form of the Triple Entry Accounting paper (original listed below) as a technical note. The tweaking was kept to a minimum so as to keep the original 2005 working paper and this 2024 published technical note aligned. Readers should be able to work with either one, the newer version only includes some very brief remarks about where blockchain fits into the framework of triple entry accounting.
Especially, readers in other languages should refer to the translations of the older working paper of 2005:
- En Español: Contabilidad por Partida Triple, gracias a Juan Ignacio Ibañez, Centre for Blockchain Technologies University College London.
- 三式记账法 (Triple Entry Accounting) in Chinese! Also, alternate location: 三式记账法 (Triple Entry Accounting) in Chinese!. Translation kindly done by shuke0327.
- La Comptabilité en partie triple (Triple Entry Accounting) in French! Translation into French by Ines Boussoffara.
- المحاسبة الثلاثية (Triple Entry Accounting) in Arabic! Translation into Arabic by Ines Boussoffara.
The 2024 publication was part of the inaugural conference on Triple Entry Accounting, for which several papers were published through a collaboration with MDPI's Journal of Risk and Financial Management. Please note that the TEA conference is asking for new papers to present in April 2025, again in cooperation with a special edition of TEA with JRFM!

Ian Grigg, On the Intersection of Ricardian and Smart Contracts
Abstract.
Bitcoin’s inclusion of the smart contract form invented by Nick Szabo has thrust this design into the forefront (Szabo, 1994). An alternate design, the Ricardian contract designed by the present author, is currently used by a few innovatory systems such as Mattereum, OpenTransactions, OpenBazaar, Askemos and CommonAccord (WebFunds, 2022).
Mark Miller sees these as two halves of a split contract, but a more popular view is to see it as an either/or choice (Walker, 1994). Which should a designer choose? Smart or Ricardian?
An analysis of both, compared, reveals that they are totally different, which begs the question, what is a contract, anyway? A contract in law is an agreement of the parties, and both of these designs fall short of entirely capturing that agreement. More importantly, the Ricardian contract captures the essence of the understanding of agreement, whereas the smart contract captures the performance of that agreement; they are two phases of a wider multi-phase project.
Then, our future goal is to incorporate both the prose of the Ricardian and the code of the smart contract, towards a fuller capture of the entire lifecycle of the contract.
Keywords: Ricardian contract, smart contract, Bitcoin
Chapter 3 in: Blockchain Technology Editor Eva R. Porras, ISBN: 979-8-88697-162-0 2022 Nova Science Publishers
This is a published edition of an older draft below.
Konstantinos Sgantzos, Ian Grigg and Mohamed Al Hemairy Multiple Neighborhood Cellular Automata as a Mechanism for Creating an AGI on a Blockchain 2022
Abstract
Most Artificial Intelligence (AI) implementations so far are based on the exploration of how the human brain is designed. Nevertheless, while significant progress is shown on specialized tasks, creating an Artificial General Intelligence (AGI) remains elusive. This manuscript proposes that instead of asking how the brain is constructed, the main question should be how it was evolved. Since neurons can be understood as intelligent agents, intelligence can be thought of as a construct of multiple agents working and evolving together as a society, within a long-term memory and evolution context. More concretely, we suggest placing Multiple Neighborhood Cellular Automata (MNCA) on a blockchain with an interaction protocol and incentives to create an AGI. Given that such a model could become a “strong” AI, we present the conjecture that this infrastructure is possible to simulate the properties of cognition as an emergent phenomenon.
Keywords: AGI; machine learning; consciousness; identity; blockchain; small world phenomenon; mandala networks; multiple neighborhood cellular automata
PDF. Local. Published by MDPI's Journal of Risk and Financial Management.
This work follows on from our previous paper below: " Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications".
Ian Grigg, Why the Ricardian Contract Came About - A Retrospective Dialouge with Lawyers
Abstract.
In the halcyon days of 1995, I needed a way to capture the nature of financial agreement in order to create an instrument that could be traded on the Internet. By way of the zero coupon bond, it was discovered that the legal prose contract is close to the semantic essence of all financial instruments; the way to issue any instrument reduces to the way to capture any contract, digi- tally and cryptographically. The “Ricardian Contract” emerged as the design pattern for that capture: a human-readable, contractually significant docu- ment, digitally signed and including sufficient but simple markup tokens such that a computer program could extract out the handful of important val- ues: face, rates, issuer, etc. The document could then be hashed cryptographi- cally, providing a secure, unique and cost-free identifier. With Bitcoin’s drive to decentralise all of finance, the design pattern is now emerging as the way to efficiently tie a legal intent into a financial agreement.
Chapter 5 in: Smart Legal Contracts Edited by: Jason Grant Allen and Peter Hunn, Oxford University Press DOI 10.1093/oso/9780192858467.003.0006
Ian Grigg
Central Bank Digital Cash -
A Credible Commitment to Privacy,
Abstract.
Central Banks are committing themselves to issue digital cash to retail or end-user customers. In so doing, they face a number of contradictions in their goals. Imposing AML, promoting financial inclusion, and not upsetting term transformation pose challenges. Riding above these challenges is the paradox of privacy: users will only respect digital cash if it is private and they feel safe in their use. This same privacy ensures that the bounty of transaction data will be a prize of great value, to be enjoyed in the breach by a host of enemies. If Central Banks do not preserve the privacy of users’ transactions, they will not adopt. As there is no easy or stable balance in privacy in such a dynamic and complex system, this is an undecidable problem, and so Central Banks must take the users’ side. To ensure success, I propose that Central Banks must provide a credible commitment to privacy, else see their designs rejected by a sceptical public.
Keywords: CBDC, Privacy Paradox, Financial Inclusion.
This paper is published in the UCL Centre for Blockchain Technologies's Discussion Paper Series : No. 8 - Q3 2022 Note that the series isn't really a peer review, and I have had substantial peer comments since then and am working an updated version here: work in progress.
Konstantinos Sgantzos & Ian Grigg Artificial Intelligence Implementations on the Blockchain. Use Cases and Future Applications 2019
Abstract
An exemplary paradigm of how an AI can be a disruptive technological paragon via the utilization of blockchain comes straight from the world of deep learning. Data scientists have long struggled to maintain the quality of a dataset for machine learning by an AI entity. Datasets can be very expensive to purchase, as, depending on both the proper selection of the elements and the homogeneity of the data contained within, constructing and maintaining the integrity of a dataset is difficult. Blockchain as a highly secure storage medium presents a technological quantum leap in maintaining data integrity. Furthermore, blockchain’s immutability constructs a fruitful environment for creating high quality, permanent and growing datasets for deep learning. The combination of AI and blockchain could impact fields like Internet of things (IoT), identity, financial markets, civil governance, smart cities, small communities, supply chains, personalized medicine and other fields, and thereby deliver benefits to many people.
Keywords: cellular automata; AGI; convolutional neural networks; intelligence augmentation; deep learning; IoT; identity; decentralized governance; personalized medicine摘要: 在深度学习领域中,有一个关于人工智能如何通过区块链成为颠覆性的技术典范。长期以来,数据科学家一直在努力维护用于机器学习数据集的人工智能实体质量。数据集的购买可能会带来非常高昂的成本,因为这取决于影响因素的正确选择以及其中包含数据的同质性,而且想要构建和维护数据集的完整性,到目前来说还算是一件困难的事情。区块链作为一种高度安全的存储介质,在维护数据完整性层面实现了技术性的飞跃。此外,区块链的不可变性与本来就需要一个高质量、永久且不断增长的深度学习数据集环境相契合,两者相互提供对方所需。人工智能和区块链的结合可能会影响诸如物联网(IoT)、身份识别、金融市场、民政、智慧城市、小型社区、供应链、个性化医疗等领域,从而造福于更多人。
关键词: 区块链;细胞自动机;AGI;卷积神经网络;智能增强;深度学习;物联网;身份识别;去中心化治理;个性化医疗
Our theoretical examination of putting machine learning transactions onto blockchains, specifically those of the Bitcoin family. PDF. Published as part of a Special Issue Blockchain: Current Challenges and Future Prospects/Applications by MDPI's journal FutureInternet.
This work follows on from the previous paper Sgantzos, K, " Implementing a Church-Turing-Deutsch Principle Machine on a Blockchain," Proceedings of the 12th Hellenic Society for Computational Biology and Bioinformatics Conference, Athens, Greece, 11–13 October 2017. Page 75! See also the following paper, "Multiple Neighborhood Cellular Automata as a Mechanism for Creating an AGI on a Blockchain," above.
Now translated into Chinese - 【翻译】区块链上人工智能的实现:用例和未来应用 at medium and 知乎 - by the inestimable 翻译@Lochaiching.
Amazingly, FutureInternet has announced that it was the most viewed paper in the last 2 years!
Ian Grigg, Response to the UKJT’s Public Consultation on crypotoassets, DLT and Smart contracts under English private law 2019
2 Enforceability of smart contracts
2.1 Principal question
In what circumstances is a smart contract capable of giving rise to binding legal obligations, enforceable in accordance with its terms (a “smart legal contract”)?
2.2 Ancillary questions
2.2.1 How would an English court apply general principles of contractual interpretation to a smart contract written wholly or in part in computer code?
2.2.2 Under what circumstances would an English court look beyond the mere outcome of the running of any computer code that is or is part of a smart contract in determining the agreement between the parties?
2.2.3 Is a smart contract between anonymous or pseudo-anonymous parties capable of giving rise to binding legal obligations?
2.2.4 Could a statutory signature requirement 12 be met by using a private key?
2.2.5 Could a statutory “in writing” requirement be met in the case of a smart contract composed partly or wholly of computer code?
A response to the UK courts public consultation on smart contracts specifically directed at the above questions (I did not response to their questions on crypto assets). In this work I was kindly assisted with incisive commentary from Judge Enrique Agudo Fernandez (Court of First Instance and Instruction, Province of Madrid, Spain)
Ian Grigg The Governed Blockchain, 2018
This paper came out of my work on the EOS blockchain, as a way to explain why the governed approach was fundamentally different, and why this was a useful direction in blockchain affairs. The concepts which derived heavily from CAcert experience can be applied to any blockchain or any community.
NortonRoseFulbright's Adam Sanitt and I collaborated on a critique on the above paper: Legal analysis of the governed blockchain (PDF). Now also translated to Chinese - Part I - 受治理区块链的法律分析 and Part II by 翻译Joey and 校对Lochaiching of EOSShenzhen Many Thanks!
Felipe De Oliveira Simoyama,
Ian Grigg,
Ricardo Luiz Pereira Bueno, and
Ludmila Cavarzere De Oliveira
Triple entry ledgers with blockchain for auditing,
IJ. Auditing Technology: Vol 3, Issue 3 2017.
This paper is published in the peer review journal International Journal of Auditing Technology, and is now open access and downloadable here: Triple entry ledgers with blockchain for auditing (PDF). Also a draft as submitted from this papers page.
Ian Grigg EOS - An Introduction, 2017
Abstract: Current technologies for blockchain fall short of providing what developers and end-users need in order to contract together and to build large scale businesses. We propose EOS, a performance-based and self-governing blockchain that provides an operating system for building large-scale consumer-facing distributed applications. This paper outlines the context, vision and software architecture underlying EOS, which we are building to serve a broad and diverse group of users with smart business.
Аннотация—Современные блокчейн-технологии вплотную подошли к тому, чтобы обеспечить разработчиков и конечных пользователей всем необходимым для заключения контрактов и создания крупномасштабных бизнесов. Мы предлагаем EOS, ориентированный на производительность самоуправляемый блокчейн, предоставляющий операционную систему для разработки крупномасштабных, ориентированных на потребителя распределенных приложений. Эта бумага описывает контекст, вИдение и программную архитектуру, закладываемую в EOS, которая строится нами для широкого круга различных применений в смарт-бизнесе.
Resumen – Las tecnologías actuales para blockchain (cadena de bloques) no logran cumplir todo aquello que los desarrolladores y los usuarios finales requieren para establecer de forma satisfactoria contratos que les permita construir negocios de gran escala. Proponemos EOS, una blockchain basada en rendimiento y en auto-gobernanza que brinda un sistema operativo para construir aplicaciones distribuidas de gran escala orientadas al consumidor. El presente documento describe el contexto, la visión y la arquitectura del software del sistema EOS que estamos construyendo para servir a un amplio y diverso grupo de usuarios con negocios inteligentes.
摘要: 前的区块链技术缺乏使终端 户与开发者连接起来的能 以及缺乏建 规模业务的技 术。因此,我们提出 EOS, 种 性能以及 治的区块链, 个 规模的 向消费者的 分布式应 操作系统。 本 概述 EOS基础的背景,愿景和EOS的底层软件架构,我们正在做的 标就是使得EOS 能为 泛和多样化的 户群提供智能商业业务。
This paper was written over the EOS.io blockchain technology. If you have comments, send them in to the normal iang @ address, or put them on the fc blog (with boring SSL drama).
These versions exist:
- Printed "black edition" has a nice black cover, distribted at FintechWeek and China meetups.
- Russian: EOS — Введение (Ян Григг) (часть 1) & (часть 2) by 🌐 Blockchained.
-
Chinese: EOS 介绍 by the Chinese EOS community! Thanks!
- Yvonne also did mindmap summary in Chinese and English.
- Spanish: EOS Una Introducción traducido por María A. Maegli y Ana I. Herrerías, with support from eosMeso! Muchisimos Gracias!
- Slides: EOS - An Introduction - Slides used in the Beijing presentation.
- Another copy is on EOS: An Introduction (eos.io copy).
Ian Grigg, Identity in Depth , 2017 published by R3.

Identity is an Edge Protocol - in that, identity as a computing system is about what one person says about another. Therefore the core of an identity system is to support reliable statements from person to person.
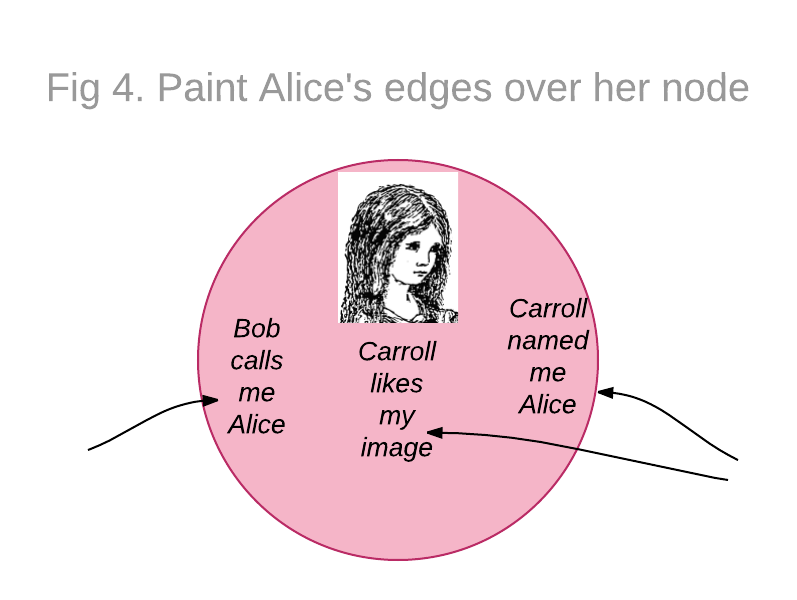
An Exploration of Identity - facing up to the Financial Identity Trilemma Syndrome requires identifying the deadly embrace of customer service, compliance and asset protection. Banks are currently squeezed by higher compliance levels, so something has to give. But is it possible to have ones cake and eat it too? This exploration explains how a customer-centric identity solution will release the banks from their trilemma.

These two essays were originally published separately as "Identity as an Edge Protocol" and "An Exploration of Identity" by the R3 consortium for financial services blockchain, and then made available as a single report Identity in Depth 3rd March 2017. They might be considered to be teasers or alternative views on Identity Cycle Alternate source: An Exploration of Identity.
Richard Gendal Brown, James Carlyle, Ian Grigg, Mike Hearn Corda: An Introduction , 2016
Abstract.
A distributed ledger made up of mutually distrusting nodes would allow for a single global database that records the state of deals and obligations between institutions and people. This would eliminate much of the manual, time consuming effort currently required to keep disparate ledgers synchronised with each other. It would also allow for greater levels of code sharing than presently used in the financial industry, reducing the cost of financial services for everyone. We present Corda, a platform which is designed to achieve these goals. This paper provides a high level introduction intended for the general reader. A forthcoming technical white paper elaborates on the design and fundamental architectural decisions.
Two of a triumvurate of articles on how the Ricardian Contract is moving forward to converge with smart contracts, and become more of a network objects design. These two 2015:
Ian Grigg, On the Intersection of Ricardian and Smart Contracts
Abstract.
Bitcoin’s inclusion of the smart contract form invented by Nick Szabo has thrust this design into the forefront. An alternate design, the Ricardian Contract designed by the present author, is currently used by a few innovatory systems such as OpenTransactions, OpenBazaar, Askemos and CommonAccord. Mark Miller sees these as two halves of a split contract, but a more popular view is to see it as an either/or choice. So let’s try that out: which should you choose? Smart or Ricardian? Let’s find out.
比特币包含由 Nick Szabo 发明的智能合约形式,这一设计被推向了目前行业中的最前沿 [ Szabo ]。而另一种设计,由本文作者[ Grigg ]设计的李嘉图合约 ,目前被一些创新系统使用,如 OpenTransactions、OpenBazaar、Askemos 和 CommonAccord [ WebFunds ]。 Mark Miller 认为这是把合约拆分为两半,但更多人的观点是倾向于将其视为一种选择 [ AMIX ]。所以让我们试试看:你应该选择哪个?智能的还是李嘉图的?让我们来看看下面的分析先吧!
This early draft has now been published in Blockchain Technology, see above. This draft also translated into Chinese by @lochaiching
Ian Grigg, The Sum of All Chains - Let's Converge!
The third paper in the triumvurate on Riccys is "Why the Ricardian Contract Came About - A Retrospective Dialoge with Lawyers" published above. Also, see my reading page and the new Wikipedia article on Ricardian contract and contribute to make it a primary introduction.
In which I apply the Ricardian Contract ideas to solving the problem of too many chains, and in the process create a network object design pattern now apparently tagged as The Ricardian Triple, which provides design direction for smart contracts, identity, IoT and chains.
Ken Griffith and Ian Grigg, Bitcoin Verification Latency - The Achilles Heel for Time Sensitive Transactions (PDF)
Abstract.
Bitcoin has a high latency for verifying transactions, by design. Averaging around 8 minutes, such high latency does not resonate with the needs of financial traders for speed, and it opens the door for time-based arbitrage weaknesses such as market timing attacks. Although perhaps tractable in some markets such as peer to peer payments, the Achilles heel of latency makes Bitcoin unsuitable for direct trading of financial assets, and ventures seeking to exploit the market for financial assets will need to overcome this burden.
As below, developments moved fast on this question, and there are now more ventures looking at the contracts and trading question. For clarification, I am the secondary author, Ken is lead. Comments can be placed on FC's announce post (in SSL only). It was written in December of 2013, and published here in Feb 2014.
Philipp Güring and Ian Grigg, Bitcoin & Gresham's Law - the economic inevitability of Collapse (PDF)
Abstract.
The Bitcoin economy exhibits remarkable and predictable stability on the supply side based on the power costs of mining. However, that stability is challenged if cost-curve assumption is not solely expressed by the fair cost of power. As there is at least one major player, the botnets, that can operate at a power-cost-curve of zero, the result is a breach of Gresham's Law: stolen electricity will drive out honest mining. This has unfortunate effects for the stability of the Bitcoin economy, and the result is inevitable collapse.
Events overtook this paper. We had hoped to present it at some interesting conference, but with the development of full-scale attacks on the Bitcoin economy, it is better out now, so as to explain the reasons. This does not preclude a later publication - this paper is still in draft in the freer sense of FC++ (comments welcome on the SSL version of the blog).
Ian Grigg An Open Audit of an Open Certification Authority
Abstract.
How does a lightweight community Certification Authority ("CA") engage in the heavyweight world of PKI and secure browsing? This talk tracks the systems audit of CAcert, an open-membership CA, as a case study in auditing versus the open Internet, community versus professionalism, quality versus enthusiasm. It will walk through the background of "what, why, wherefore an audit," look at how CAcert found itself at this point, and then walk through some big ticket items: risks/liabilities/obligations; assurance and what's in a name; disputes and reliance; and systems and security.
Can CAcert deliver on its goal of free certs? The audit is into its 3rd year as of this writing; and remains incomplete. Some parts are going well, and other parts are not; by the end of the year 2008, we should be able to check all of the important areas, or rethink the process completely. Hence, finally, the talk will close with progress and status, and recommendations for the future.
Presented as an invited talk at the 22nd Large Installation Systems Administration Conference (LISA 2008) 13th November 2008. Above is HTML with slides embedded within; also available are the slides in extracted form. See also the CAcert and the audit page.
Ian Grigg The Market for Silver Bullets (pdf)
Abstract. As a “good” in the sense of economics, security is now recognised as being one for which our knowledge is poor. As with safety goods, events of utility tend to be destructive, yet unlike safety goods, the performance of the good is very hard to test. The roles of participants are complicated by the inclusion of agressive attackers, and buyers and sellers that interchange.
This essay hypothesises that security is a good with insufficient information, and rejects the assumption that security fits in the market for goods with asymmetric information. Security can be viewed as a market where neither buyer nor seller has sufficient information to be able to make a rational buying decision. Drawing heavily from Michael Spence's “Job Market Signaling,” these characteristics lead to the arisal of a market in silver bullets as participants herd in search of best practices, a common set of goods that arises more to reduce the costs of externalities rather than achieve benefits in security itself.
This paper is part of a group of papers emerging from an investigation into Information Security and Signalling. This is a difficult paper, and is advancing slowly, but I think its proposals are very important. See also the (complete) Pareto-Secure paper below.
Ian Grigg The Ricardian Contract
Abstract. Describing digital value for payment systems is not a trivial task. Simplistic methods of using numbers or country codes to describe currencies, and ticker tape symbols to issue bonds, shares, and other financial instruments soon run into shortcomings in their ability to handle dynamic and divergent demands. The seemingly arbitrary variations in the meanings of different instruments are best captured as contracts between issuers and holders. Thus, the digital issuance of instruments can be viewed as the issuance of contracts.
This paper proposes that the contract is the issue. A document form is described that encompasses the inherent contractual nature of the financial instrument yet copes with the requirements of being an integral part of a payment system.
Abrégé Décrire la valeur numérique pour systèmes de paiement n’est pas une tâche insignifiante. Les méthodes simplistes de l’utilisation des nombres ou des codes du pays afin de décrire les devises et les symboles des télex pour émettre les obligations, les actions et les instruments financiers bientôt confrontés à des lacunes par rapport à leur capacité d’endurer la divergence et dynamicité des exigences. Les variations apparemment arbitraires concernant les significations des différents instruments sont capturées en tant que contrats entre émetteurs et détenteurs. Par conséquent, l’émission numérique des instruments pourrait être considérée comme l’émission des contrats.
Le présent document traite de la question du contrat : Un formulaire du document est décrit en tant qu’un qui comprend la nature intrinsèque du contrat de l’instrument financier. Cependant, il fait face au besoin d’être une partie intégrale du système de paiement.
摘要: 描述支付系统的数字价值并不是一项简单的任务。使用数字或国家代码来描述货币的简单方法,以及用于发行债券、股票和其他金融工具的代码很快就会遇到处理动态和不同需求的能力方面的缺陷。不同工具的含义看似随意的变化最好是可以被视为发行人和持有人之间的合约。因此,工具的数字发行可以看作是合约的发行。
本文提出的合约是发行。描述了一份文件表格,其中涵盖了金融工具的固有合约性质,但是却符合作为支付系统不可或缺部分的要求。
ملخص
إن وصف القيمة الرقمية لأنظمة الدفع ليس بالامر الهين .قد تفشل الآليات المبسطة لإستخدام الأرقام أو رموز البلدان لوصف عملات ورموز التلكس لإصدار السندات والأسهم والأدوات المالية في قدرتها على معالجة المطالب الدينامية والمتباعدة.والواقع أن الاختلافات التعسفية ظاهرياً في معاني مختلف الأدوات يمكن إبرامها باعتبارها عقوداً بين الجهات المصدرة و أصحاب العملات. وبالتالي يمكن النظر إلى الإصدار الرقمي للصكوك على أنه إصدار عقود. وتقترح هذه الوثيقة أن يكون العقد هو المسألة. ويرد وصف لنموذج الوثيقة الذي يشمل الطابع التعاقدي الاصيل للصك المالي ولكنه يتفي مع ذلك متطلبات أن يكون جزءا لا .يتجزأ .من نظام الدفع
Kindly presented by Mark Miller at First IEEE International Workshop on Electronic Contracting, (WEC) 6th July 2004. Above is HTML, original submitted in multicolumn DOC form. also available is PS.
Now translated and available:
- 李嘉图合约 (The Ricardian Contract) in Chinese! Translation into Chinese kindly done by 初译Fred and 校对Lochaiching.
- LE CONTRAT RICARDIEN (The Ricardian Contract) in French! Translation into French by Ines Boussoffara.
- العقد الريكاردي (The Ricardian Contract) in Arabic! Translation into Arabic by Ines Boussoffara.
See also the reading page and the new Wikipedia article on Ricardian contract. Please contribute to make it a strong introduction.
Abstract. What do people mean when they say something is secure?
Shamir's 1st law says absolute security does not exist, yet the popular press and the security buying process is inundated in secure product. For some of these products, there may be merit in the term, but for many it is more debatable. Such differences of meaning and applicability suggest low efficiency in the market for security, as well as a blackspot on the claim for security as a robust science.
One way to define 'secure' is to apply the economics theory and terminology of Pareto efficiency. This simple structure gives an easy way to categorise and choose among alternates, and identifies when an optimum has been reached. We suggest that this meaning may already be in wide spread usage, intuitively, among security practitioners and the popular press.
Pareto-Secure was one of the three papers presented in the founding issue of Advances in Financial Cryptography . As editor, publisher and chief gopher that was an easy decision for me! FC++ as it is known for short is a pre-publication drafts circle designed to polish our work before going out to a 'real publication'.
Abstract. The digitally signed receipt, an innovation from financial cryptography, presents a challenge to classical double entry bookkeeping. Rather than compete, the two melded together form a stronger system. Expanding the usage of accounting into the wider domain of digital cash gives 3 local entries for each of 3 roles, the result of which I call triple entry accounting.
This system creates bullet proof accounting systems for aggressive uses and users. It not only lowers costs by delivering reliable and supported accounting, it makes much stronger governance possible in a way that positively impacts on the future needs of corporate and public accounting.
Resumen
El recibo digitalmente firmado, una innovación de la criptografía digital, presenta un desafío a la clásica contabilidad por partida doble. Más que competir, la unión de ambas resulta en un Sistema más fuerte. Expandir el uso de la contabilidad hacia el dominio más amplio del dinero digital resulta en 3 registros locales, uno para cada uno de 3 roles, al resultado de lo cual denomino contabilidad por partida triple.
Este esquema crea sistemas contables a prueba de balas para usos y usuarios agresivos. Al ofrecer una contabilidad confiable y respaldada, no solamente reduce los costos, sino que además posibilita una gobernanza mucho más fuerte, en una forma que impacta de manera positiva en las necesidades futuras de la contabilidad corporativa y pública.Résumé
Le reçu signé numériquement, une innovation de la cryptographie financière, présente un défi à la comptabilité classique en partie double (à double entrée). Plutôt que de concurrencer, les deux étant fusionnés forment un système plus solide. L’extension de l’utilisation de la comptabilité dans le domaine plus large de la trésorerie numérique donne trois entrées locales pour chacun des trois rôles dont le résultat j’appelle la comptabilisation en partie triple. Ce système crée des systèmes de comptabilité à l’épreuve des balles pour les utilisations et les utilisateurs agressifs. En outre, Il permet non seulement de réduire les coûts en fournissant une comptabilité fiable et soutenue, mais aussi de renforcer la gouvernance d’une manière qui influe positivement sur les besoins futurs de la comptabilité ministérielle et publique.摘要: 数字签名收据是金融密码学的一项创新,它对传统的复式记账法提出了挑战。 使这两者结合而非相互竞争,能够形成更强大的体系。将会计的使用范围扩大到数字现金的更广泛领域,为3个角色提供了3份本地记录,我称之为三式记账法( triple entry accounting). 该系统为激进的用途和用户提供了无懈可击的(bullet proof)会计系统。它不仅提供可靠的会计支持降低成本,而且使得更强有力的治理成为可能,从而对企业和公共会计的未来需求产生积极的影响。
:ملخص
يمثل الاستلام الموقّع رقمياً تحدياً وذلك مع العلم أنه إبتكار من الترميز المالي.وبدلاً من المنافسة، ينصهر الاثنان معاً في هيئة نظام أقوى.. إن توسيع نطاق استخدام المحاسبة في مجال النقد الرقمي الأوسع يمنح 3 إدخالات محلية لكل من الأدوار الثلاثة و بالتالي يمكن تسميتها بالمحاسبة بالقيد الثلاثي. و يقوم هذا النظام بإنشاء أنظمة محاسبة مقاومة للرصاص من أجل الاستخدامات والمستخدمين العدائيين.فهو لا يعمل على خفض التكاليف من خلال توفير حسابات موثوق بها ومدعومة فحسب، بل إنه يجعل من الحوكمة الأكثر قوة أمراً ممكنا وذلك على نحو يؤثر إيجابيا على احتياجات المحاسبة .العامة والشركات مستقبلا
An attempt to meld our ground-breaking digital issuance innovations with classical accountancy. In Financial Cryptography it is an article of faith that double entry bookkeeping has taken a broadside from the digital certificate, and is expected to sink any year now. Instead, I look at how the two can work together and emerge stronger for their contributions.
Now translated and available:
- En Español: Contabilidad por Partida Triple, gracias a Juan Ignacio Ibañez, Centre for Blockchain Technologies University College London.
- 三式记账法 (Triple Entry Accounting) in Chinese! Also, alternate location: 三式记账法 (Triple Entry Accounting) in Chinese!. Translation kindly done by shuke0327.
- La Comptabilité en partie triple (Triple Entry Accounting) in French! Translation into French by Ines Boussoffara.
- المحاسبة الثلاثية (Triple Entry Accounting) in Arabic! Translation into Arabic by Ines Boussoffara.
Triple Entry Accounting was one (which earnt lots of comments) of the three papers presented in the second issue of Advances in Financial Cryptography .
James Nesfield and Ian Grigg Mutual Funds and Financial Flaws
Abstract. Mutual funds are vulnerable to abuses involving market timing and late trading. Primarily, this is due to a failure of governance, and the delayed nature of settlement of both payments and transfers. This vulnerability is only exploited over time, through a progression of small steps that, individually, raise no alarm, but in sum, cross the line of acceptable behaviour. Solutions to the abuses will be found not in more regulation, but in open governance and a move towards real time gross settlement.
This paper was submitted as testimony to the U.S. Senate's finance subcommittee during hearings on the mutual funds scandal (dead link?) , 27th January 2004. Above is HTML, original submitted in PDF form (local and also senate copy), also available is PS. Also see the in-person testimony before the hearings.
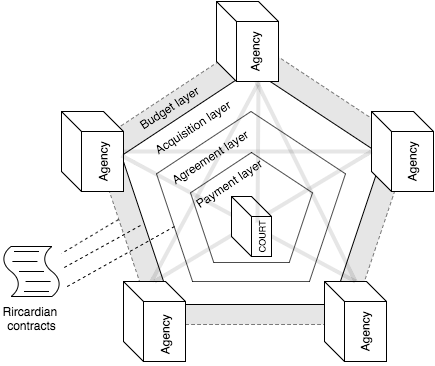
Ian Grigg Financial Cryptography in 7 Layers
I seek to reduce complexity by presenting Financial Cryptography in a 7 layer model. This model separates the field into distinct disciplines of Finance, Value, Governance, Accounting, Rights, Software Engineering, and Cryptography. I also present Systemics' Ricardo system in the light of this model, as an example.
The paper was presented at Financial Cryptography 2000 (FC00) and was originally published in the Proceedings of Financial Cryptography Fourth International Conference, FC 2000 Anguilla, British West Indies, February 21-24, 2000, Springer-Verlag LNCS 1962. Here is the postscript.
Ian Grigg Digital Trading
I survey the current state of the art in digital trading and brokerages. I also document some of Systemics' experiences in digital certificate trading, and draw the conclusion that future trading will be open and costless. This predicted future may not come pass, but it will serve as a benchmark for the financial world as it enters into an era of rapid and dramatic structural change.
It was presented at the first Digital Money conference, London, October 1997, and appeared in the November 1997 issue of Virtual Finance Report . Here is the postscript.
Ian Grigg and C Petro Using Electronic Markets to Achieve Efficient Task Distribution
This is our controversial proposal to automate the division and distribution of labour. Where Marx has failed, Markets can succeed! By allocating ownership of software projects as fungible units, we seek to use digital value systems to assist in raising funds for open source software.
It was presented at Financial Cryptography 1997 (FC97) and was originally published in the Proceedings of Financial Cryptography First International Conference, FC'97 Anguilla, British West Indies, February 1997. Springer-Verlag LNCS 1318. Here is the postscript.
Ian Grigg, Critique on the 1994 EU Report on Prepaid Cards
A viewpoint on what's happening in the European Internet Cash policy arena, and why it represents a bad move for Europe.
published in The Journal of Internet Banking and Commerce , Vol 2, Num 2 March 1997. For more information on the European debate, see my Money Page. Here is the postscript.
Ian Grigg, The Effect of Internet Value Transfer Systems on Monetary Policy
Abstract: The arisal of experimental systems to transfer value (digital cash) over the Internet is of interest to monetary policy circles. These systems claim to turn the International Financial System back to the days of free banking, with uncontrolled and rampant issue of currency by private banks. This paper argues that, in actuality, Internet cash issuance will not be a strong force, neither against the tools of monetary policy, nor for its own mercantile purposes.
Three models are used to develop an understanding of how digital cash systems will fit in the financial system. Fractional banking describes the effect of such cash on the money supply. The Baumol-Tobin model provides insights into how digital cash will function in terms of balances, and thus how it effects the rest of the financial system. Finally, a look at potential participancy reveals the scale of effect on monetary policy.
摘要: 货币政策界对通过互联网转账(数字现金)的实验系统的兴起表现出兴趣。这些系统声称由于目前私人银行不受控制且猖獗地发行货币,国际金融系统将会回到了自由银行的时代。本文认为,实际上,互联网现金的发行既不会成为强大的冲击,也不会不利于货币政策工具,更不会出于实现自身的商业目的。 我们将使用三种模型来解释数字现金系统是如何适合金融系统的。部分银行描述了这种现金对货币供应量的影响。 Baumol-Tobin 模型提供了关于数字现金将如何在余额方面发挥作用的见解,以及它如何影响金融系统的其他内容。最后,看一下潜在的参与程度,进一步揭示出对货币政策的影响程度。
This paper was written in April-June 1996 as primary assessment for Professor Michael Kuczynski's International Financial Systems elective in the London's MBA programme. The paper argued that Internet cash issuance would not be a strong force, neither against the tools of monetary policy, nor for its own mercantile purposes. As it was a hot topic at the time, and this was only the second paper on the subject, I published it on the web.
And now, after 24 years !!! we have a translation into Chinese. 互联网转账系统对货币政策的影响 on medium and 知乎 and 简书 . Translation done by the unstoppable @Lochaiching! As CBDCs are now a hot topic following Libra, and China is leading the world in CBDCs with the first major planned issuance of a CBDC, this paper perhaps has new relevance for its prediction. Here is the postscript.